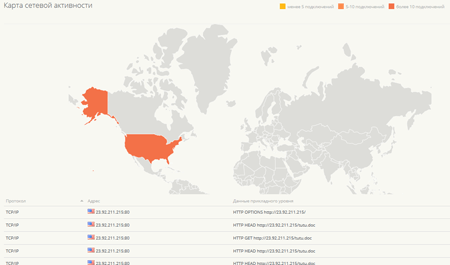
Network activity map
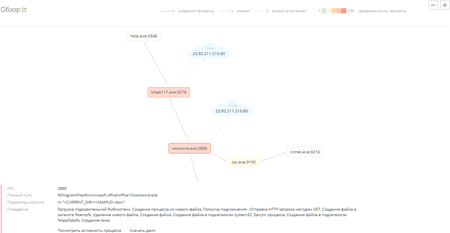
When launched in a virtual environment, a malicious program will expose itself and try to reach other nodes on the local network and the Internet. In the network activity section of the report page, you will see the location of the hosts the analysed program has been trying to reach.